A few years ago, we were called in to handle a serious incident at a company dealing with financial operations. The company needed to resolve an infiltration issue that, under normal circumstances, should never have occurred. The attack was not targeted, it was not particularly sophisticated, and the attacker likely knew very little about the company. It was a typical opportunistic attack, the kind that floods the internet today… and yet, in our client’s environment, it caused unprecedented disruption. All it took was a single unsecured entry point exposed to the outside world.
A vulnerability in the JetBrains TeamCity tool quickly became part of automated internet scans shortly after it was published. Our client’s server was among those that responded to this “digital radar,” and suddenly everything started moving. The attacker exploited the weakness, deployed malware, and established a communication channel to a command-and-control server, from which further instructions were received. Within hours, scheduled tasks, system services, and eventually even a remote management tool were added.
From the attacker’s perspective, the result was an incredible success. They gained full access to the server with root privileges, the ability to work with data, keys, and internal systems. From the company’s perspective, however, nothing seemed to be happening. No alerts were triggered, no warnings appeared, and consequently, no response was initiated. The incident only surfaced when it was already necessary to deal with its consequences.
The foundation is a secured perimeter and protected endpoints
The technology company, which relied on dozens of virtual servers for its operations, was not notable for what it had in place to protect against external attacks, but rather for what it lacked. There was no firewall, no segmentation, and no endpoint monitoring. If a perimeter firewall had been in place, it would have restricted or completely blocked access to the vulnerable service. At the same time, the company lacked any solution capable of monitoring endpoints within the network, which could have detected suspicious behavior as soon as it began. The combination of these two layers would have, with high probability, stopped the attack before it had a chance to develop into anything harmful.
The incident was not an example of a sophisticated hack, but rather a demonstration of how even a simple attack can cause significant damage when basic security measures are missing. The company we helped clean up the situation, suddenly had no issue investing substantial amounts into security tools and measures.
“Kybernetická bezpečnosť je dnes komplexná disciplína s množstvom nástrojov a prístupov, no v praxi sa opakovane potvrdzuje, že všetko stojí na niekoľkých kľúčových vrstvách,” vysvetľuje Jakub Koštial, expert na implementáciu technológií z firmy Binary Confidence. Notebooky, servery či pracovné stanice predstavujú miesto, kde sa reálne vykonáva škodlivá aktivita. Tu sa spúšťajú procesy, manipulujú sa dáta a dochádza k eskalácii oprávnení. “Ak firma nemá prehľad o tom, čo sa deje na úrovni level, in practice, it has no idea it has been compromised until it is too late,” he adds.
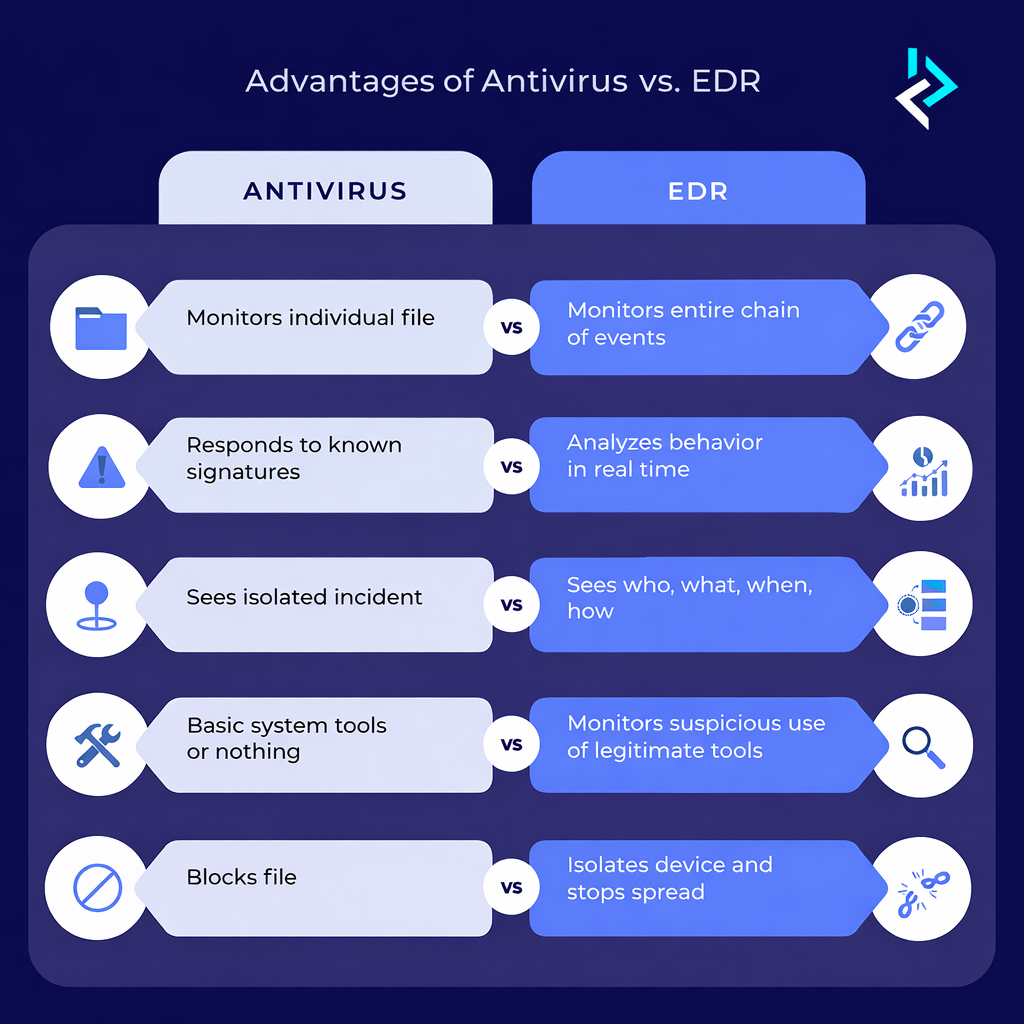
Modern solutions such as ESET, SentinelOne or Palo Alto Cortex XDR therefore do not only serve to detect known malware, but analyze system behavior in real time. They can identify anomalies, attempts at persistence, or communication with suspicious servers and respond to them immediately. Without this layer, an organization is effectively blind. Modern endpoint solutions go beyond legacy antivirus and provide an active level of protection.
A firewall, on the other hand, represents the first line of defense between internal infrastructure and the internet. Its role is not just to “allow or deny” traffic, but to actively control what enters the network and under what conditions. In an environment where services are often exposed online, a properly configured perimeter is essential.

Technologies from vendors such as Palo Alto Networks or Fortinet today enable deep traffic inspection, threat identification, and application control. A firewall is an active security component capable of blocking attacks before they ever reach their target systems.
Not everything needs to be replaced. Make the most of what you already have!
Many companies already own the necessary technologies. However, the mere presence of a tool does not mean it is being used effectively. Proces implementácie technológií by nemal byť o ich nákupe, ale mal by sa začať pochopením prostredia, pokračovať návrhom vhodného riešenia a vrcholiť konfiguráciou. How the system is set up largely determines whether it produces meaningful insights or just noise. A poorly configured system may ignore critical threats, while it should be stopping attacks at their earliest stage.
The assumption that higher security automatically requires new purchases is, according to Jakub Koštial, one of the most common misconceptions. “In practice, we repeatedly see organizations that have high-quality technologies, but lack proper configuration, integration, or understanding of their capabilities. At Binary Confidence, we approach security pragmatically and in a vendor-agnostic way.”

We respect the client’s existing technology stack and aim to optimize it so that it makes sense within their specific environment. New solutions are recommended only when they truly bring added value. This approach allows organizations to achieve a higher level of security faster, more efficiently, and without unnecessary costs. Importantly, it does so without significantly disrupting business operations.
What can we deliver?
The incident described at the beginning was not exceptional and highlights something we encounter quite often, as also confirmed by statistics. A global survey from last year indicates that up to 20% of companies operate without any form of security. More than half of organizations are aware they are potential targets, yet only a quarter entrust their security management to professionals. There are, however, relatively simple solutions that can significantly improve your security through financially and operationally efficient enhancements.
“Keď u nášho klienta postavíme základy, implementácia môže zvyčajne prirodzene pokračovať smerom k plnohodnotnému bezpečnostnému ekosystému. Cieľom pritom nie je mať „čo najviac nástrojov“, ale vytvoriť funkčný, prepojený organizmus, ktorý dokáže reagovať na reálne hrozby,“ vysvetľuje Jakub Koštial. Implementáciu technológií preto netreba vnímať ako jednorazový projekt, ale pokojne aj ako dlhodobý proces, ktorý dáva vaším draho nakúpeným technológiám zmysel. At the same time, it is important to remember that implementation alone is not enough—if you want the highest level of security assurance, continuous monitoring and ongoing management are essential..
List of technologies we can deploy as part of our implementation services:
Endpoint protection
- ESET
- SentinelOne
- Palo Alto Cortex XDR
Network security
- Palo Alto Networks
- Fortinet
SIEM and log management
- Elastic
- IBM QRadar
- Palo Alto XSIAM
Threat Intelligence
- Recorded Future
- Hudson Rock
SOAR and automation
- Palo Alto XSOAR
- Vulnerability management
- Rapid7
- vScan
Data Leak Prevention
- Trellix
Infrastructure monitoring
- Zabbix
Honeypots
- Cowrie
- Dionea
- Suricata
![]()
The project funded through grant agreement number 101145856 is supported by the European Cybersecurity Competence Centre.